In this series, I explore the history of information security or what later became the history of cybersecurity. These posts are the English translations of the podcast episodes that will be published alongside this, but (unfortunately) in German. I am not sure yet how many episodes will come out in total. Throughout this history of cyber security series, I anticipate covering one or a maximum of two decades per episode/blog post, providing a comprehensive and engaging exploration of IT security history. However, as the field evolves, I know that more significant events may arise, potentially challenging the planned format. Each episode/blog post will be structured along 4 chapters:
Chapter 1 focuses on the historical context and events that have shaped IT security. From the release of groundbreaking technologies to significant attacks, the invention of concepts, and the passing of crucial laws, this chapter delves into the facts and milestones that have defined each decade.
In Chapter 2, we will dive into the computing context of each period. It is important to understand how computers were used in the past, as it directly influences security implications. Computers were utilized in vastly different ways than today, and I aim to remind you of those differences.
Moving on to Chapter 3, we will explore the development of threats in the IT landscape. Characterizing these threats is essential in comprehending the evolving challenges of IT security over time.
Finally, Chapter 4 delves into the evolution of IT security measures. From technical and organizational strategies to policies, concepts, and even legal or political interventions, we will examine the measures taken to enhance security.
Chapter 1: The early days of IT Security
When exploring the history of IT security, we could consider various starting points. For instance, the history of cryptography can be traced back to the Romans, or to discussions about ciphers in the Middle Ages and Renaissance. Alternatively, the history of IT security could begin with the history of early calculating machines in the Renaissance. However, I have chosen to commence the history of IT security in the 1940s for two compelling reasons. First, this is when the first digital computers were developed and second, the security context of the Second World War influenced the development of computer security.
Significant innovations of the 1940s: Mainframes, Bugs, and manual programming
The 1940s marked a pivotal era in the history of IT security. This decade witnessed the introduction of significant technological advancements that laid the foundation for modern IT security practices.
In 1940, Bell Telephone Laboratories introduced their first computer, enabling remote calculations via a teletype terminal. Concurrently, the Bombe computer, designed by Alan Turing, was employed to crack the German encryption machine Enigma, playing a pivotal role in World War II. Three years later, in 1943, German engineer Konrad Zuse completed work on the Z3, a pioneering computer utilizing 2300 relays and punched film for code storage. Despite being destroyed by Allied bombs during the war, a replica of the Z3 exists in the German Museum in Munich. Additionally, the Mark 1, a room-sized, relay-based computer, was completed at Harvard in the same year, further advancing computing technology.
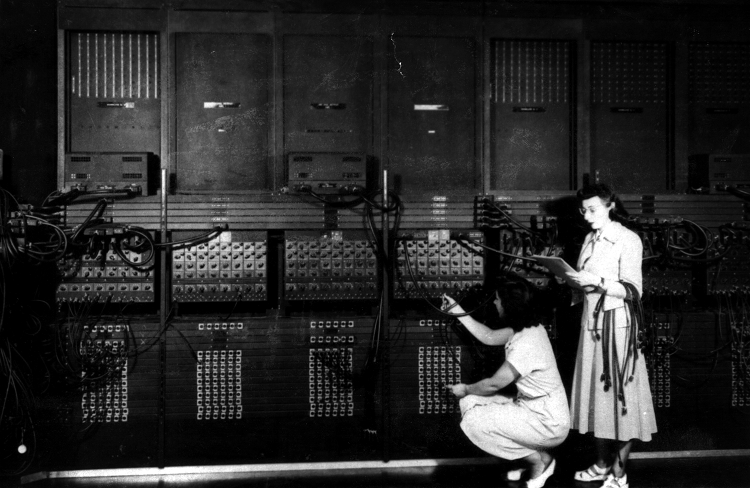
The unveiling of the ENIAC computer in 1946 represented a significant leap forward in computing technology, with over 18,000 vacuum tubes, a clock frequency of stunning 5000 Hz, and a weight of 30 tons. This marked a pivotal moment in the development of early computing systems. In 1947, programmer Grace Hopper discovered the first computer bug when she found a moth stuck between the relay contacts of the Harvard Mark 2, leading to the popularization of the term „bug“ to refer to computer errors. The year 1948 saw the publication of Norbert Wiener’s influential book „Cybernetics,“ in which he coined the term „cyber“ and emphasized the importance of understanding the world in terms of information and interconnected feedback loops (hear my first podcast episode on this here, german). This laid the groundwork for the conceptualization of cybernetics and its relevance to the field of IT security. Furthermore, in 1948, researchers at the University of Manchester, including Williams, Kilburn, and Toothill, developed the Small-Scale Experimental Machine (SSEM), also known as the „Manchester Baby.“ This marked a significant advancement in electronic storage for computers, as it was built to test a new storage technology developed by Williams and Kilburn, known as the Williams Tube, which was the first high-speed electronic storage for computers. They also ran one of the first more complex computer programs on it, consisting of seventeen instructions, making it the first program in history to be executed on a digital, electronic, stored-program computer.
Chapter 2 Context & computer operations: Switchboards, wires, and punch cards
The use of computers in the 1940s and 1950s differed dramatically from today. And with this different usage, came different IT security or cybersecurity requirements. For example, the programming of the ENIAC involved a combination of switches, cables, and plugboards, which were manually configured to set up the computer for specific tasks and calculations. This process required a deep understanding of the hardware and operation of the computer, and it was labor-intensive and time-consuming, as the computer had to be manually reconfigured for each new task. This had to be laid out in theory first. Programmers wrote their programs on paper, which often took weeks. Then the switches and wires had to be adjusted on the machine to run the program. This could take days to implement. The input and output systems of that time typically consisted of punch cards or punched tape with encoded data, and jobs were processed in batches or stacks. In other words, someone intentionally injecting malicious code into these systems was unlikely to happen. Accidental mishaps and bad code were way more likely.

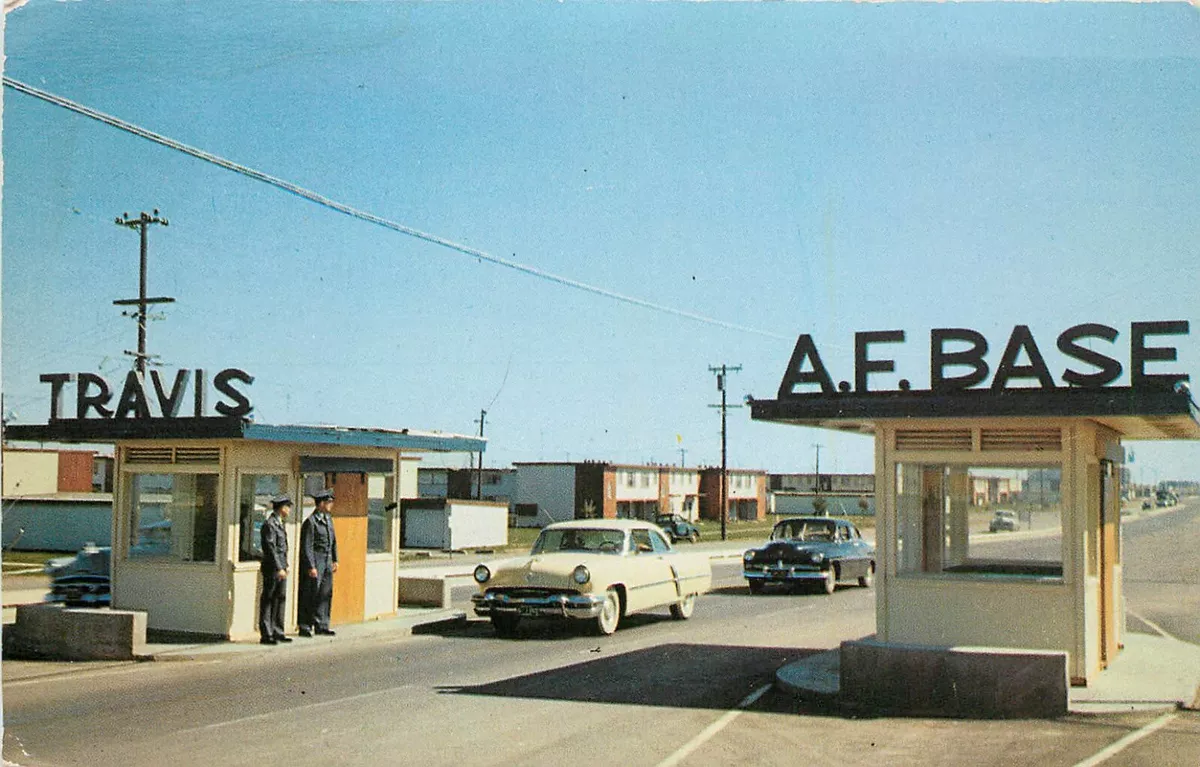
The people who used computers were few and consisted of specially trained personnel, engineers, and scientists. The early computer operators were often women. Researchers wanting to run programs often had no physical contact with the computers performing their calculations. The few computer operators that existed were subjected to relatively strict security checks before being allowed access to the computers. Of course, many of these machines were operated in a military context on military bases where the general public had no access.
Chapter 3 Threats: Insiders, informants, and traditional espionage
The 1940s marked a significant era in the development of computing and security practices in the history of cybersecurity. During this time, the primary IT security threats were insiders, double agents, and traditional espionage. A notable example is the Manhattan Project, where security was crucial to keep the entire atomic weapons program secret from Germany and Japan. However, Soviet spies infiltrated the project, sending critical information back to Russia and likely accelerating the Soviet acquisition of an atomic bomb by at least 12-18 months. This highlighted the significant security risks posed by espionage during this period. For example, several Russian informants and spies penetrated the research nuclear facilities at Los Alamos. At Los Alamos, the MANIAC 1 computer was developed by physicist Nicholas Metropolis, based on the computer architecture developed by John von Neumann. This computer played a crucial role in performing complex mathematical and scientific computations for the Manhatten project. If Russian spies were aware of these machines or even had access, is unknown, but it highlights the theoretical risks of espionage.

Another security risk of computers at that time was electromagnetic radiation. Electronic radiation or emission posed potential computer security risks for early mainframes. For example, if a cipher machine was not electromagnetically shielded from the input machine carrying the plaintext, echoes of the unencoded message could be transported along with the encrypted message through the output cables. This became a particular concern in the 1950s, leading to the establishment of the first standard called TEMPEST for the acceptable level of emissions when processing classified information. TEMPEST encompassed technologies that suppressed signal emissions from electronic devices, including physical shielding and the generation of additional radiating devices to generate „noise“ to make eavesdropping on the signals more difficult. However, implementing such measures became increasingly challenging over time as computers became smaller in the 1950s and 1960s, and the number of computers increased, leading to more „open“ environments. The lack of uniformity in security measures persisted until the establishment of the first Industrial Tempest Program (ITP) in 1974, which also targeted companies.
Chapter 4 Security: IT security = physical security
During the 1940s, the focus of computer security was primarily on physical security, which was an integral part of the broader security of the facilities where the computers were housed. Cybersecurity was not a separate discipline. Security protocols were designed to prevent or combat theft, vandalism, sabotage, and natural disasters such as hurricanes, floods, tornadoes, volcanoes, and earthquakes. This encompassed the use of security personnel such as guards, fences, and alarms to prevent unauthorized personnel from entering facilities, reflecting the emphasis on safeguarding the physical infrastructure housing the computers. Computers were often located at military bases so the physical security was generally tighter compared to other institutions. In most bases, access is controlled by guard posts keeping access control lists of authorized military personnel on a base. This practice shielded the computers from unauthorized access.
However, data security was also a growing concern during this period. The US Executive Order 8381 of March 22, 1940, introduced the well-known classification system for classified data, such as „top secret,“ which was previously stamped on files. This system, known as Mandatory Access Control (MAC), allowed specifically authorized or privileged decision-makers to define the classification level of documents. Only individuals with the appropriate authorization and security clearance were allowed to access and read these documents. MAC remains one of the most important cybersecurity practices, even today, and is implemented at the operating system level, with administrators defining access for users based on the confidentiality of data and user clearance levels.
The historical development of cyber security, spanning from the 1940s to the present day, provides valuable insights into the foundations of modern cybersecurity practices and the ongoing efforts to safeguard computing systems and information.
Chapter 5: 1950s and the road ahead
However, the 1950s marked a turning point as several key innovations emerged. In 1951, UNIVAC introduced the „UNISERVO“ tape drive, the first tape drive for a commercial computer, which offered portability and unlimited offline capacity. This enabled the transport of more data in „relatively“ small enclosures. In 1953, MIT’s Whirlwind became the first computer to use magnetic core memory, a significant advancement in storage technology. Additionally, researchers at MIT began experimenting with direct keyboard input to computers, laying the groundwork for the operating modes commonly used today. The introduction of FORTRAN, a powerful scientific programming language, revolutionized coding and enabled the generation of more efficient code. This made programming much simpler compared to the traditional adjustment of switches and cables. The 1950s also saw the first experiments with computer networks, exemplified by IBM’s SAGE (Semi-Automatic Ground Environment), which facilitated real-time communication between computer centers across North America. The SAGE system interconnected Radar sites in the US and was part of the early warning system against Soviet nuclear bombers. Based on their espionage, the Russians were able to copy the design of the American nuclear bomb and became a nuclear power in the late 1940s. Furthermore, in 1958, Jack Kilby’s invention of the integrated circuit, or microchip, revolutionized the commercialization and miniaturization of computers, paving the way for future technological advancements. In terms of IT security, not much changed in the 1950s compared to the 1940s. It becomes more interesting in the next episode as a new mode of computing is introduced, which was already heralded by the SAGE system: multi-user timesharing.
Sources
- Computer History Timeline, https://www.computerhistory.org/timeline/1947/
- Meijer/Hoepman/Jacobs/Poll (2007), Computer Security Through Correctness and Transparency, in: de Leeuw/Bergstra, The History of Information Security: A Comprehensive Handbook, Elsevier.
- Yost (2007), A History of Computer Security Standards, in: de Leeuw/Bergstra, The History of Information Security: A Comprehensive Handbook, Elsevier.
- DeNardis (2007), A History of Internet Security, in: de Leeuw/Bergstra, The History of Information Security: A Comprehensive Handbook, Elsevier.
- Brenner (2007), History of Computer Crime, in: de Leeuw/Bergstra, The History of Information Security: A Comprehensive Handbook, Elsevier.
- Biene-Hershey (2007), IT Security and IT Auditing Between 1960 and 2000, in: de Leeuw/Bergstra, The History of Information Security: A Comprehensive Handbook, Elsevier.
- Espionage and the Manhattan Project, https://www.osti.gov/opennet/manhattan-project-history/Events/1942-1945/espionage.htm